Cyber Security
Protect your business from cyber threats, secure your endpoint, application, network and internet connectivity for enterprise and service provider.

Infrastructure Security
Infrastructure security is vital because it safeguards critical systems, data, and operations from cyberattacks and physical threats. It ensures business continuity, protects sensitive information, and maintains trust with customers and partners. Failure in infrastructure security can result in significant financial losses and reputational damage.
We provide infrastructure security solutions for both north-south traffic and east-west traffic. Currently, We provide services using a variety of devices and solution to meet your needs, starting with DDOS Protection , NGFW, IPS, PAM, IAM

Next Generation Firewall (NGFW)
We provide enhanced security by combining traditional firewall capabilities with advanced features like deep packet inspection, intrusion prevention, web filtering and application-level control. We offer real-time threat detection and prevention, reducing the risk of data breaches and cyberattacks.

Next Generation-IPS (NG-IPS)
As cyber attacks evolve, network security requires unparalleled visibility nd intelligence covering all threats for comprehensive protection. With differing organizational responsibilities and agendas, you need a consistent security enforcement mechanism. These increasing operational demands call for a renewed focus on dedicated Secure IPS to provide a deeper level of security and visibility for the enterprise.

DDoS Protection
We provide top-tier automatic DDoS stateless solutions for all types of organizations and service providers. Adapting to the more sophisticated, multi-vector DDoS attack and volumetric attack. Our solution protect you and your customers’ services with our on-premises, stateless solution that automatically detects and intelligently mitigates DDoS attacks and other cyber threats. A cloud-based, fully managed DDoS protection service with scrubbing centers worldwide.

Privileged Access Management (PAM)
Secure privileged credentials and secrets with comprehensive capabilities for OS, endpoints, cloud infrastructure and workloads, servers, databases, applications and more. Centralized policy management allows administrators to set policies for password complexity, frequency of password rotations, and store log of either command line and video to quickly identify any malicious activity for admin to take action.

Identity and access management (IAM)
Manages the end-to-end lifecycle of user identities and entitlements across all enterprise resources, both in data centers and in the cloud. In short, with IAM, you can centrally manage permissions that control which resources users can access.

Network Access Control (NAC)
Provides robust network access control with granular role-based policies for authentication, authorization, continuous monitoring and enforcement. NAC solution provides oversight of all devices in use across the organization, it enhances security while authenticating users and devices the moment they enter the network. In addition, immediate action can be taken against unauthorized or unusual behavior can be reduced.
Application Security
Application security helps protect modern and hybrid applications against advanced and multi-vector attacks regardless of where they are running.
With real-time threat detection and proactive defenses, our solutions provide unmatched protection. Choose us to enhance your security and empower your organization to thrive securely in today’s dynamic cyber environment.

WEB & API Security
Web applications and application programming interfaces (APIs) are business-critical technologies which are prime targets for cyberattacks. From malware and cross-site scripting to adversarial bots and volumetric DDoS campaigns, more threats to web apps and APIs grow more every year.
Our Web and API protection solution delivers intelligent, end-to-end protection against a wide range of multi vector attacks. With automatic API discovery, adaptive detections, built-in bot mitigation, and continuous self-tuning.

Email Security
Protect organizations from all types of email threats, such as phishing, ransomware, zero-day attacks and business email attacks. Our solution leverages AI-powered security services that help maximum security to prevent, detect and respond to email threats in real time.

Database Security
Database Security automatically discovers databases on the network and in the cloud. Our solution can identify and classify sensitive data. It also help organizations unleash the power of their data by reducing the risk of non-compliance or a security breach incident. We can scan your databases for vulnerability to help you keep your databases covered for the latest threats.

Data Loss Prevention ( DLP )
We help your business to discover, classify, monitor and protect data intuitively with zero friction to the user experience. Audit behavior in real-time with Risk-Adaptive Protection to stop data loss before it occurs. Elevate your data security strategy with us safeguard your sensitive information and avoid unintentional loss of valuable data.
It is easy to deploy and manage across your entire IT infrastructure whether your data is in the cloud or on-prem from a single console.
End Point Security
Endpoint security is the process of protecting devices that connects to the corporate network from being exploited by malicious actors and campaigns. Endpoint security has evolved from traditional antivirus software to providing comprehensive protection from sophisticated malware and evolving zero-day threats.

Endpoint Detection and Response (EDR) / Extended Detection and Response ( XDR )
EDR is a comprehensive endpoint security solution that provides real-time threat detection and response capabilities, automated incident response and forensic investigation capabilities.
Enhancement from EDR arrive to XDR solutions which unify security-relevant endpoint detection with telemetry from security and business tools such as network analysis and visibility (NAV), email security, identity and access management, cloud security and more.
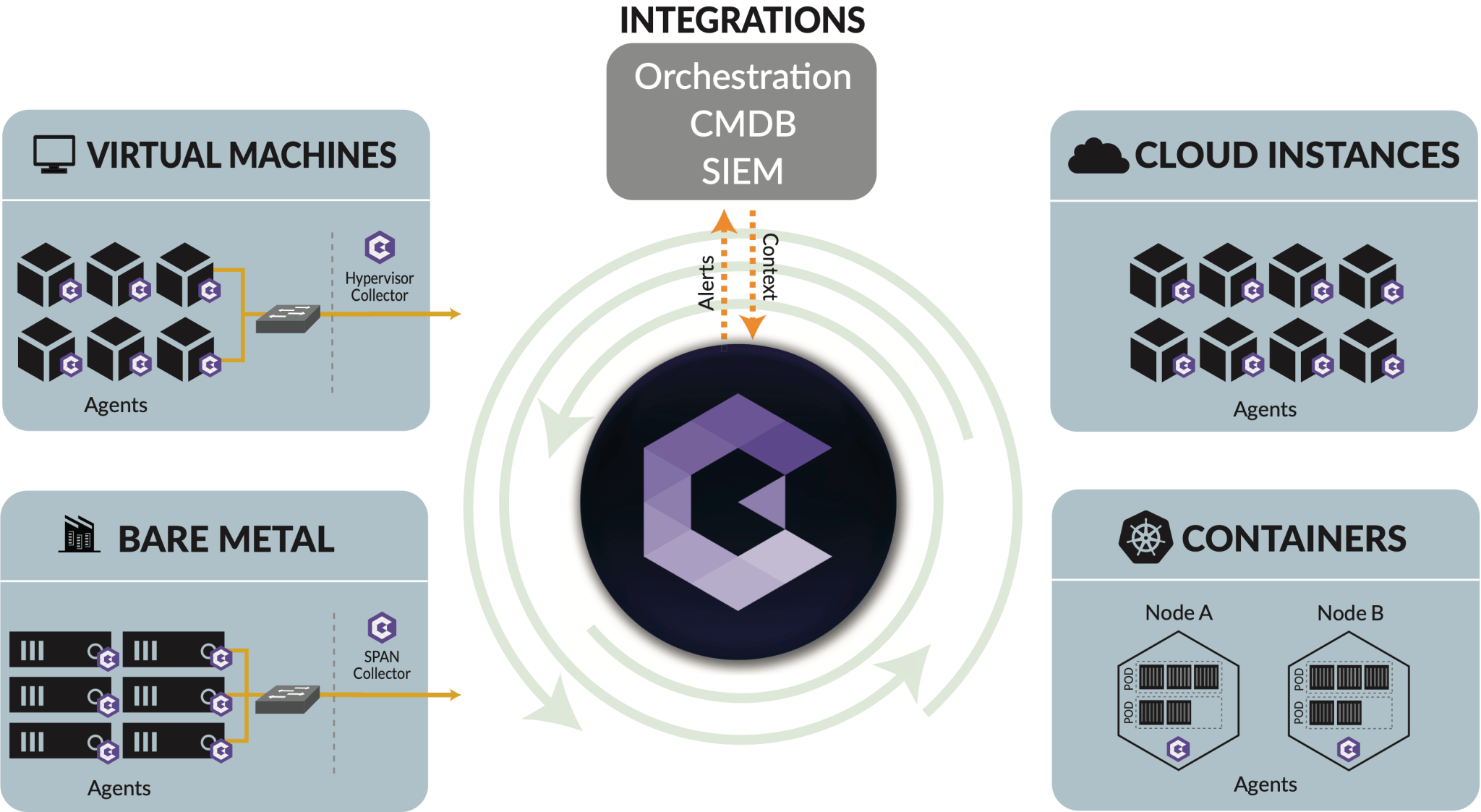
Micro Segmentation
Micro segmentation approach to the granular control of application and workload visibility to delivery security by dividing the network into isolated segments.
Our solution provide simplest, fastest and most intuitive way. It enables you to prevent malicious lateral movement in your network through precise segmentation policies, visuals of activity within your IT environment and network security alerts.
Zero Trust Security
Zero Trust is a security framework by eliminating implicit trust and continuously validated for security configuration and posture before being granted or keeping access to applications and data where they are located, for users working from anywhere.
Security Operation
Security operation is essential part of every organization nowadays. It is no deny that security operation help organize and safeguard its assets, people, data, and facilities against various threats and risk. It cover wide range of practices including information security, incident and response plan, ongoing monitoring, vulnerability management and policy enforcement.
Our tools will help your security measurement and protection of your IT infrastructure become more efficient.

Security Information and Event Management (SIEM)
Security information and event management, or SIEM, is a security solution that helps organizations recognize and address potential security threats and vulnerabilities before they have a chance to disrupt business operations. SIEM systems help enterprise security teams detect user behavior anomalies and use artificial intelligence (AI) to automate many of the manual processes associated with threat detection and incident response.

Security Orchestration, Automation and Response (SOAR)
SOAR is a comprehensive security orchestration, automation and response (SOAR) platform that unifies case management, automation, real-time collaboration and threat intel management to serve security teams across the incident lifecycle.
















