Network Infrastructure
Network Infrastructure
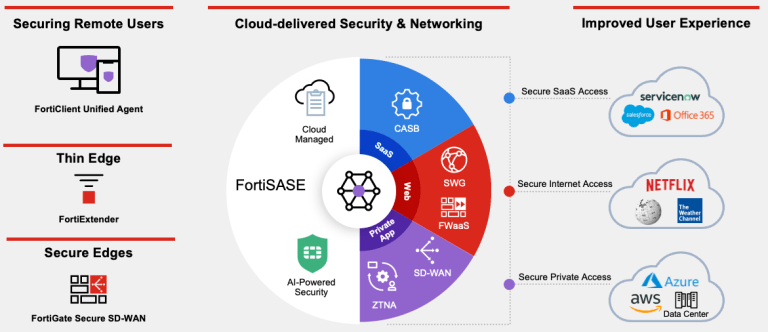
Cyber Security
Cyber Security
Datacenter
Datacenter
Network and Application Monitoring
Network and Application Monitoring
Voice
Voice
Cloud
Cloud
Whatever you trying to do, we will be there with you on every step of the way
Latest updates from our partners
Latest from Fortinet
Curious about Fortinet’s News Releases? Please come check out our News Releases and updates. We highly suggest you read them today.
- Fortinet Deepens Integration to Uniquely Secure Enterprise AI at Scale with NVIDIAon May 12, 2026 at 1:00 pm
- Fortinet Reports Strong First Quarter 2026 Financial Resultson May 6, 2026 at 8:05 pm
- Fortinet Expands FortiGate G Series to Secure AI from the Data Center to Modern Enterprise Edgeson May 6, 2026 at 1:00 pm
- The Fortinet 2026 Global Threat Landscape Report Reveals a Surge in AI-Enabled Cybercrime, Contributing to a 389% Increase in Ransomware Victims Year-over-Yearon April 30, 2026 at 1:00 pm
- Fortinet Returns to Join Global Leaders at the World Economic Forum Annual Meeting on Cybersecurity 2026on April 29, 2026 at 1:00 pm
Fortinet Blog
Explore the latest cybersecurity trends and innovations, leading edge threat intelligence from FortiGuard Labs, Fortinet executive insights, and customer perspectives.
Latest from Netscout
Checkout news and latest update blogs from Netscout
- Black Box Versus Glass Box DDoS Protectionby MIke Wetherbee on June 11, 2026 at 1:00 pm
Distributed denial-of-service (DDoS) attacks continue to grow in scale, frequency, and sophistication, forcing organizations to rethink not just how they defend against attacks, but how much visibility and control they have over those defenses. At the center of this shift is a fundamental architectural choice: black...
- Intellyx Names NETSCOUT to Prestigious 2026 Digital Innovator Award Listby Eileen Haggerty on June 9, 2026 at 12:42 pm
Earning industrywide recognition two years in a row is very rewarding. Achieving that same honor six consecutive times makes a statement. Being selected by Intellyx for its 2026 Digital Innovator Award as an industry disruptor and innovator is a validation of NETSCOUT’s long-held commitment to blazing new trails. At...
- How to Operationalize Threat Hunting with NETSCOUT, SIEM, XDR, EDR, and SOARby Robert Derby on June 4, 2026 at 12:05 pm
Threat hunting does not fail because security teams lack tools. It fails because the tools are often used as separate workspaces instead of connected parts of the same investigation. A security information event management (SIEM) or extended detection and response (XDR) solution collects and correlates events. Endpoint...
- Solving Network Blind Spots Created by Massive Data Silosby Anthony Cote on June 3, 2026 at 1:00 pm
“Dump everything first, structure it later” is a risky data migration strategy. In a large enterprise, moving petabytes across a network is nerve-racking and expensive, so many increasingly move applications, analytics, and processing closer to where the data already resides. That’s a trap. Software engineer Dave...
- The Self-Healing Network: Why Your AI Strategy Needs a Neutral Lensby Agnes Mends-Crentsil on June 2, 2026 at 1:35 pm
In the race to 5G-Advanced and 6G, the “self-healing network” has moved from a whiteboard concept to a boardroom mandate. For next-generation networks, the promise is clear: an autonomous infrastructure that predicts failures before they impact the bottom line and remediates them without human intervention. But as...
Latest from Dell
Here are the latest news from Dell!!
- Building Dell Technologies’ First Ever Global Internship Experienceon June 11, 2026 at 2:00 pm
Inside Dell’s first global internship: meaningful work, real connections, and the launchpad turning interns into future leaders worldwide.
- XREAL Rips the Hardware Out of Mixed Realityon June 11, 2026 at 1:00 pm
How XREAL shipped nearly 1M augmented reality glasses by removing what Apple and Meta kept adding.
- Dell Pro Webcams: AI Imaging, Secure Login, Smarter Collaborationon June 10, 2026 at 4:00 pm
AI imaging, secure sign‑in, smarter sharing. Meet Dell Pro 7 Webcam 4K and Pro 5 Webcam 2K for clearer meetings anywhere.
- When Architecture Fights Gravity, Operations Pay the Tax.on June 10, 2026 at 1:00 pm
Why “unified namespace” is a polite way of pretending data has no mass, and what the three forms of data actually let you move.
Latest from Akamai
Checkout what happening with Akamai
- Keep Your Tech Flame Alive: Trailblazer Rachel Bayleyby Akamai FLAME Team on June 11, 2026 at 10:31 pm
In this Akamai FLAME Trailblazer blog post, Rachel Bayley encourages women to step into the unknown and to be their authentic selves.
- Threats Making WAVs - Incident Response to a Cryptomining Attackby Guardicore Labs Team on June 11, 2026 at 10:31 pm
Guardicore security researchers describe and uncover a full analysis of a cryptomining attack, which hid a cryptominer inside WAV files. The report includes the full attack vectors, from detection, infection, network propagation and malware analysis and recommendations for optimizing incident response processes in data centers.
- The Oracle of Delphi Will Steal Your Credentialsby Daniel Goldberg on June 11, 2026 at 10:31 pm
Our deception technology is able to reroute attackers into honeypots, where they believe that they found their real target. The attacks brute forced passwords for RDP credentials to connect to the victim download and execute a previously undetected malware, which we named Trojan.sysscan.
- The Nansh0u Campaign – Hackers Arsenal Grows Strongerby Ophir Harpaz & Daniel Goldberg on June 11, 2026 at 10:31 pm
In the beginning of April, three attacks detected in the Guardicore Global Sensor Network (GGSN) caught our attention. All three had source IP addresses originating in South-Africa and hosted by VolumeDrive ISP (see IoCs).